Interesting Reading Material

How Someone Can Steal My Credit Card Informatio...
An electronic pickpocket can steal things off of your RFID-enabled devices with ease. By using a concealed RFID reader, a person can gather information on RFID chips from several feet...
How Someone Can Steal My Credit Card Informatio...
An electronic pickpocket can steal things off of your RFID-enabled devices with ease. By using a concealed RFID reader, a person can gather information on RFID chips from several feet...
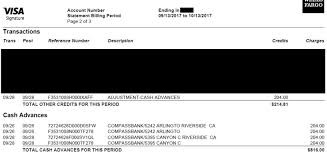
Identity Theft Protection Tips: Always Review Y...
Take a look at your monthly statements to see how your credit cards are being billed. Look for any suspicious charges that you might not recognize. You can ask to...
Identity Theft Protection Tips: Always Review Y...
Take a look at your monthly statements to see how your credit cards are being billed. Look for any suspicious charges that you might not recognize. You can ask to...
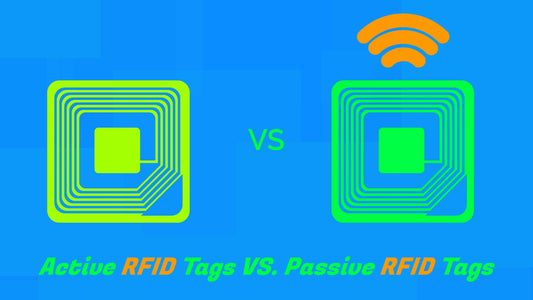
Understanding RFID Technology
To know what makes electronic pickpocketing work, it helps to see how the technology works, to begin with. The RFID or Radio Frequency Identification system is a popular layout for...
Understanding RFID Technology
To know what makes electronic pickpocketing work, it helps to see how the technology works, to begin with. The RFID or Radio Frequency Identification system is a popular layout for...
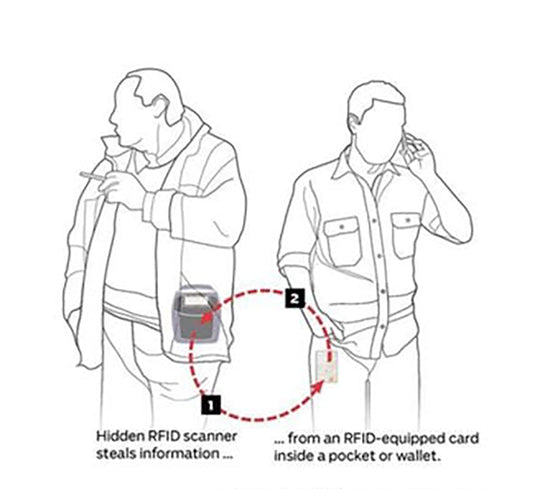
What Is Electronic Pickpocketing and How Do You...
Electronic pickpocketing is a legitimate concern for all people to watch for. RFID technology makes card less or cashless payments easy to handle. But even with that, it also introduces...
What Is Electronic Pickpocketing and How Do You...
Electronic pickpocketing is a legitimate concern for all people to watch for. RFID technology makes card less or cashless payments easy to handle. But even with that, it also introduces...
